Disk Utility User Guide
- Disk Image .dmg Does Not Ask For Password When Encrypted File
- Disk Image .dmg Does Not Ask For Password When Encrypted Mean
When you format an internal or external storage device, you can encrypt and protect it with a password. If you encrypt an internal device, you must enter a password to access the device and its information. If you encrypt an external device, you must enter the password when you connect the device to your computer.
If you encrypt an external storage device, you can’t connect it to an AirPort base station for Time Machine backups.
John The Ripper: Cracking a.DMG Let's cut to the chase right now: Cracking encrypted disk image, AKA DMG is feasible, but, and there are many buts, is extremely, extremely time consuming. I encrypted a folder and forgot to save the password. Took about 3 hours to fully install. Upon the start up I was given the Migration Option to which I chose to migrate from my Encrypted(By the High Sierra install) SSD drive. Fortunately for me when it asked for the FileVault password, I used the password for my user account (this also worked to mount the disk in diskutility). Simply Select 'AES-128' under the 'Encryption' drop-down menu. After you click 'Create' and it will ask you to create a password for your files. If you add the password to your key chain, you will not have to enter your password to access the.dmg file when logged into your account.
WARNING: To encrypt and protect the device with a password using Disk Utility, you must erase the device first. If the device contains files you want to save, be sure to copy them to another storage device or volume.
If the device contains any files you want to save, copy them to another storage device or volume.
In the Disk Utility app on your Mac, choose View > Show All Devices.
If Disk Utility isn’t open, click the Launchpad icon in the Dock, type Disk Utility in the Search field, then click the Disk Utility icon .
In the sidebar, select the storage device you want to encrypt.
Click the Erase button in the toolbar.
Enter a name for the volume.
Click the Scheme pop-up menu, then choose GUID Partition Map.
Click the Format pop-up menu, then choose an encrypted file system format.
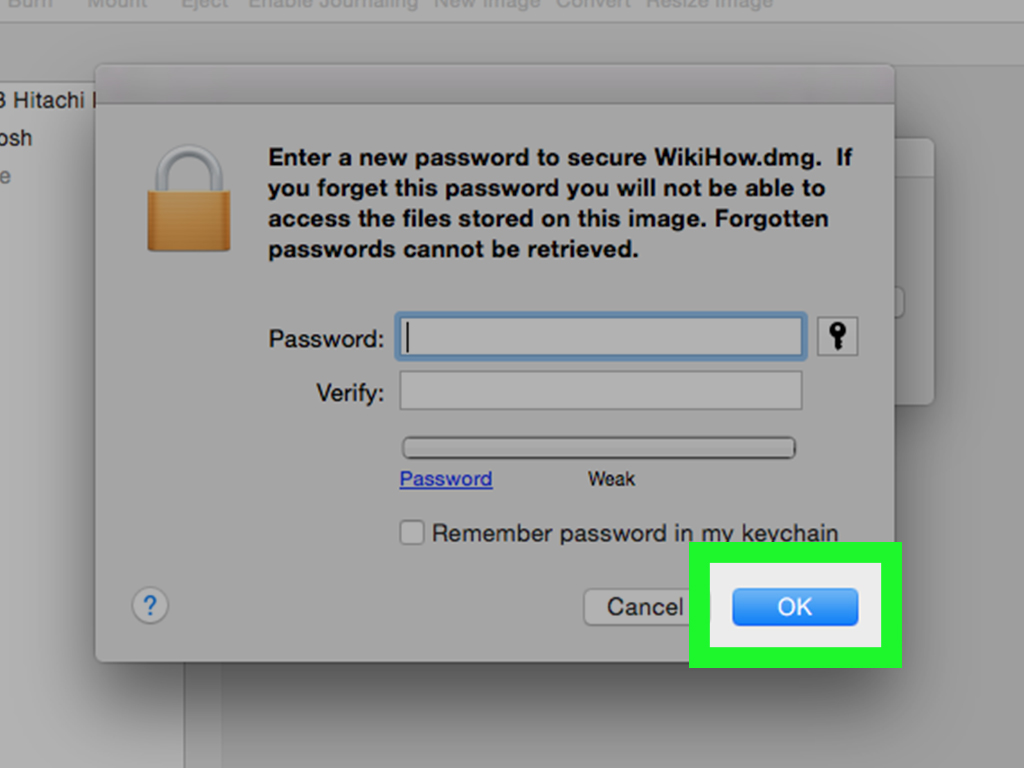
Enter and verify a password, then click Choose.
To change the password later, select the volume in the sidebar, then choose File > Change Password.
(Optional) If available, click Security Options, use the slider to choose how many times to write over the erased data, then click OK.
Secure erase options are available only for some types of storage devices. If the Security Options button is not available, you can’t use Disk Utility to perform a secure erase on the storage device.
Click Erase, then click Done.
You can encrypt your data without erasing it by turning on FileVault in the Security & Privacy pane of System Preferences (see Encrypt Mac data with FileVault).
You can also encrypt a disk and protect it with a password without erasing it. See Encrypt disks or memory cards to protect your Mac information.
I like to tinker with encryption, not because I have any real use-case for it, but because I find the entire subject enjoyable.
Just thought I’d take a moment to share with you the bit I was working on tonight: A symmetric (passphrase) encrypted disk image usable on Mac, Linux, and Windows.
WARNING: I am in no way responsible if you do something to break your data or your computer. Make sure passphrases you use are accurate and you can remember them, there is no way to recover an encrypted file without them.
First up: Create the disk image, I chose ExFAT as the filesystem as it is reasonably portable and standardized on as the filesystem for SDCards means out of the box support on most systems (including Raspberry Pi). I’m using .dmg as the file extension because Mac requires it on creation. Feel free to use whatever suits you.
Creating the disk image
Creating the disk image on Mac:
Creating the disk image on Linux:
Creating the disk image on Windows:
On Mac you can double-click the file, or type open <filename> or open disk utility and use file -> open. On Linux you may be able to double-click in some desktop applications, but you can always mount it with mount -t exfat -o loop <filename> <mount directory>
Encrypting the disk image
I use GPG Keychain on Mac, which allows me to simply right click the file and then use Services -> OpenPGP: Encrypt File and then uncheck any keys in the main section and check the Encrypt with password box in the lower left.
The commandline option will work under Mac or Linux with GPG installed. I’ll do an article on getting GPG installed at some point in the future and try to remember to link it in here.
This will prompt you to enter a passphrase, which will be converted to an appropriately sized key. The -s is optional, it will also sign it with your private key so that it can be verified during decryption. If you get the following error, you don’t have a private key set up for signing and can not use -s.
On Windows… right click and hope your GUI has an encrypt function? I’ve got a Windows computer around here somewhere… I’ll try to figure it out later.
Once encrypted you can share it as needed. Depending on your goal you may want to additionally delete the original (non-encrypted file) after you’ve done some verification. How much verification you do will depend on how paranoid you are, this is a good step, though gpg -d encrypted-file.gpg | cmp - original-file.dmg
Decrypting the disk image
This is the easy part, on Mac and Windows and many Linux Desktops: Simply double-click and you will be presented with a box asking for a password. After decryption is complete, if you signed the file with -s, it will pop up a notice telling you that the signature has been verified and you know that the contents were extracted correctly.
The command line method is:
If all goes well you’ll get output like:
Disk Image .dmg Does Not Ask For Password When Encrypted File
You can now mount the disk image just like in the Creating the Disk Image section.
Final Words
Disk Image .dmg Does Not Ask For Password When Encrypted Mean
These encryption and decryption instructions will also work with any individual file. For small files you can even do fun things like not use --armor instead of -o <output filename>and get output to the terminal in ASCII text, suitable for including in e-mail or the like.
However, I really actually recommend just encrypting the files with your own key as a recipient in general. As long as you have your private key, then you can access the disk image, file, or whatever. If you are sending the file to someone else you should encrypt it using their public key as the recipient so that they can easily decrypt it. Symmetric encryption is for the times that you are encrypting it for your own use in a case where you will have access to GPG, but potentially not to your own private key.
